API Endpoint
API Endpoint Support and Management
Comprehensive Interface Inventory: Through automated tools, it comprehensively scans and records API interfaces in business systems, supporting multiple types of API interfaces such as RESTful, SOAP, CoAP, XML-RPC, etc. It can analyze business access traffic in real-time, dynamically organize API asset purposes and changes, helping to quickly identify new, unknown, and deprecated API assets.
API Vulnerability Monitoring
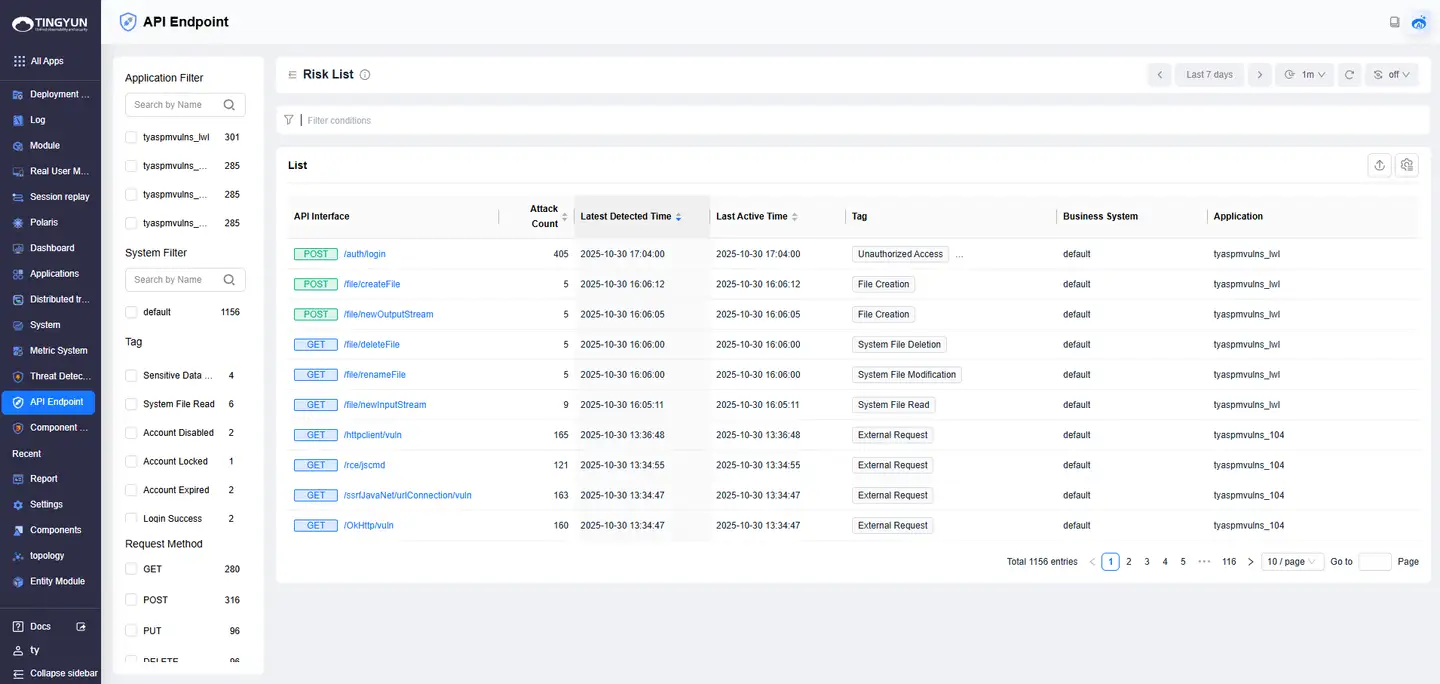
Risk Behavior Monitoring: Built-in behavior risk automatic monitoring engine that provides real-time monitoring and alerts for user abnormal API data access behaviors, utilizing machine learning algorithms to learn common attack behaviors on API interfaces, accurately identifying API interface attack behaviors and abnormal access behaviors, supporting traceability to trace back to data breach sources.
API Security Protection
Automated Blocking and Protection: Provides automated blocking for the latest request times of API assets and various attack behaviors, helping enterprises respond to sudden traffic and malicious attacks, protecting backend resources from overload and abuse.
Sensitive Data Protection: Based on application traffic analysis and advanced graph model technology, it automatically identifies sensitive data in API interfaces and performs inventory classification. Built-in sensitive data identification rules intelligently identify various sensitive parameter information to prevent sensitive information leakage.
API Behavior and Status Monitoring
Unauthorized Access Monitoring: Can identify unauthorized access behaviors of APIs, through traffic analysis reconstruction and sensitive data identification labeling, providing real-time monitoring of user abnormal data access behaviors.
Outbound Connection Behavior Monitoring: Monitors outbound connection behaviors of APIs to ensure API usage complies with security standards.
System Sensitive Command Monitoring: Identifies behaviors where APIs execute system sensitive commands, preventing malicious exploitation of APIs to attack systems.
Activity Monitoring: Through API traffic analysis, it provides an overview of enterprise API assets, API activity levels, API sensitivity involvement, API risk events and change trends, helping enterprises visually manage API full lifecycle protection, timely detect and handle threats.